The State of Critical Infrastructure Resilience
Cyber threats pose a growing risk to utility operators—and public safety.
Cyberattacks on water and power put the public at risk
How prepared are providers of water and electricity to detect, respond to, and recover from cyber threats? Attacks are on the rise, and even short disruptions of these critical services can cause widespread social and economic harm.
The State of Critical Infrastructure Resilience reveals crucial lessons for publicly and privately operated utilities.
Utility systems are under threat
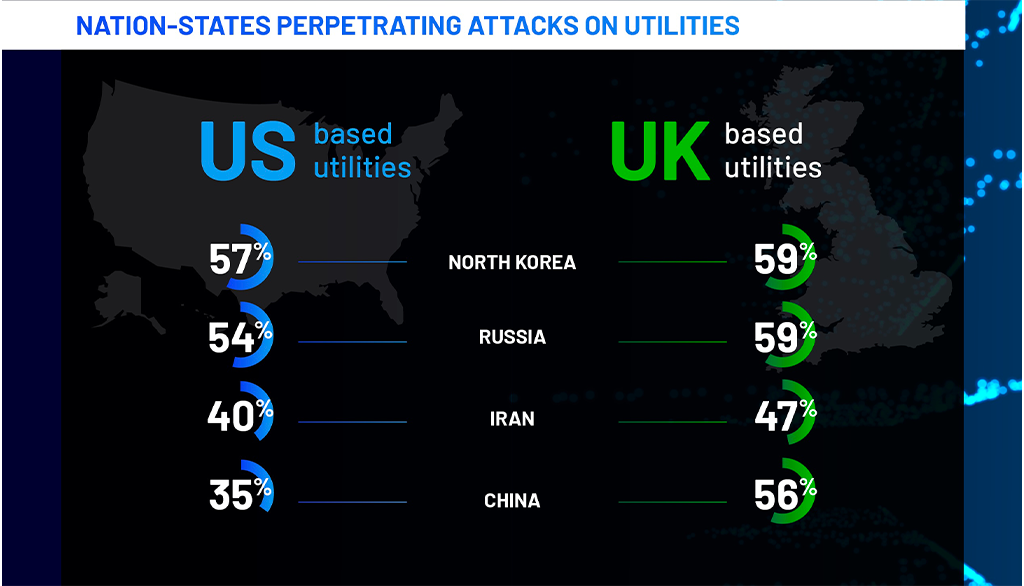
Whether they aim to extort money, conduct espionage, or gain political leverage, nation-state threats see infrastructure attacks as a golden opportunity. Experts agree that attackers’ motivations might spur a demand for ransom—or an attempt to remain undetected and instead plant backdoors or exfiltrate data.
“Many public utilities likely don’t realize that China has infiltrated their infrastructure,” notes Chris Inglis, former US National Cyber Director and Semperis Strategic Advisor.
Critical infrastructure demands operational resilience
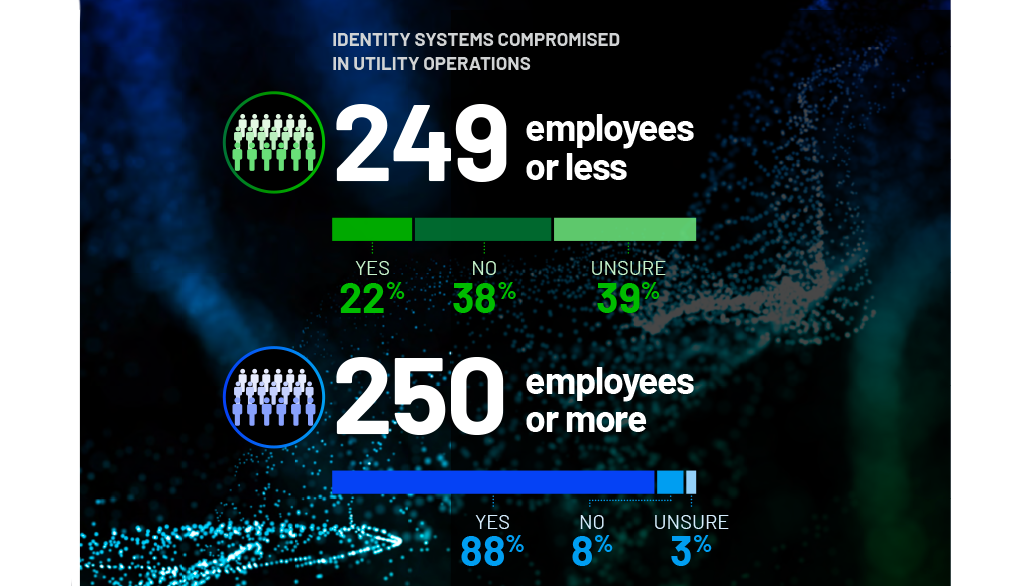
Operators of critical infrastructure services should make operational resilience a top priority. Today’s complex cyber threat landscape demands a proactive approach to resilience—one that assumes breach and readies the organization to respond to and recover from any threat that might interrupt its mission. For nearly every organization, this means securing the resilience of the identity infrastructure.
The critical role of identity systems—such as Active Directory (AD), Entra ID, and Okta—in authentication and authorization have made them a top attack target. Attackers use identity compromise to move laterally and escalate their privileges in the breached environment or take down Active Directory to cripple the organization; without a functional AD, users cannot log in and resources cannot be accessed.
More resources
Learn more about how to prevent, detect, and respond to identity-based attacks.